Data breaches are far deeper than what appears on the surface. They are not just temporary terrors but can leave a long-lasting impact on the person or the organization. A data breach is the intended exposure of sensitive/confidential data to an untrusted environment by an unauthorized individual or organization for personal gains. In common terms, it can be called a data leak or data spill. The severity depends on the type of information leaked and on the victim.
Data breaches are often used to seek revenge or blackmail a rival for various purposes. The rate of data breaches is increasing rapidly, and it’s now not a matter of if it happens but when it happens. This blog will delve into your first steps towards mitigating a data breach and how to avoid data from being leaked.
What Is a Breach Notification?
The probability of a data breach happening is very high nowadays. A company’s Cyber Insurance team and Risk Management team are essential to address this probability, as they can calculate and determine a breach with an accuracy of 90%. Data breaches are on the rise because most data is now stored on the cloud and digital storage units. The probability of a data breach hitting an organization is inevitable.
Being prepared beforehand and having a response plan ready to reduce the aftermath of a data breach can save the organization from huge financial losses and minimal data loss. The most commonly used attacks in data breaches are phishing, malware attacks, ransomware attacks, and DDOS attacks.
A data breach literature survey conducted in the year 2019 shows that 64% of Americans have not checked if they have been affected by major data breaches. 56% confessed that they wouldn’t know what to do if they were victims of a data breach attack. It is important to notify the victim whose data was affected in a data breach attack and hire lawyers specialized in the field to help the victims with various legal concerns. 48 states in the U.S. have Breach Notification laws which state that the victim whose data was involved in the attack should be notified.
The European Union General Data Protection Regulation (GDPR)has laws relating to data breaches. Article 34 states that “When the personal data breach is likely to result in a high risk to the rights and freedoms of natural persons, the controller shall communicate the personal data breach to the data subject without undue delay.”
Data breach laws differ from country to country and have different stances, and it is always advised to seek legal counsel if your organization is dealing with a data breach.
If the breach has data related to Protected Health Information (PHI), one should evaluate if the Health Insurance Portability and Accountability Act (HIPPA) Notification Rule can be applied. The HIPPA Notification Rule details the steps and measures to be taken. A Breach Notification report can be done by summing up all the necessary information about when the breach took place, what kind of data was compromised, if the motives were known, etc.
How to Respond to a Breach
After discovering unauthorized data access (data breach), the first and foremost priority is to incorporate the incident response plan to minimize the damage as much as possible. Analyze what kind of data was breached (specifically which data), when it happened (time frame), whom the data belongs to, etc. The following are the steps to be taken within 48 hours of a data breach:
◉ Try to contain the breach. Time is essential in such crucial situations, and hence it’s important to try to stop the breach as early as possible. The type of the breach and the systems infected are responsible for determining the methods used to contain the breach.
◉ Isolate the systems (source) responsible for the breach. This prevents the malware or virus from spreading.
◉ Freeze all the data transmission and cut off any incoming or outgoing data internally and externally.
◉ Confirm that logging is going on to track all the entries and actions taking place.
◉ Determine the impact of the data breach and work on solutions to reduce the damage.
◉ Communication is key during such incidents. Communicate with the required internal personnel to explain the breach and its course, analyze the situation, and plan a better solution.
◉ Update the response plan and the recovery plan incorporated with better solutions to prevent any kind of attack.
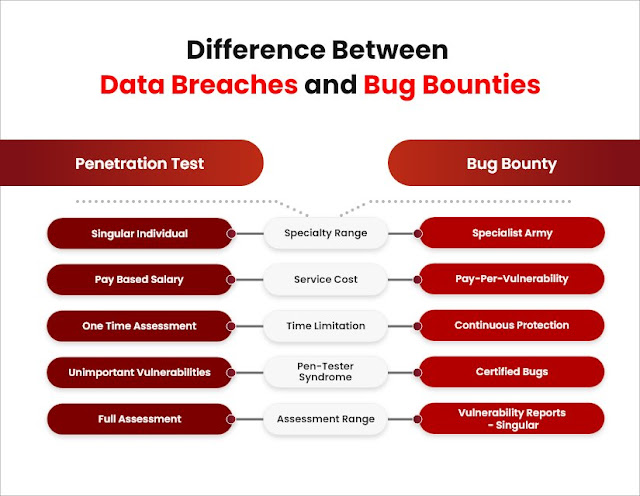
Difference Between Data Breaches and Bug Bounties
A data breach is the compromising of confidential/sensitive data, whereas a bug bounty is a program that helps in the identification of a vulnerability that can prevent data breaches. The differences between the two must be understood to have a clear perspective.
A bug bounty program authorizes the participants to infiltrate the platform to identify vulnerabilities. This is not considered a data breach as the company authorizes it and the program has certain rules to be followed. Anyone found violating the rules of the program will be disqualified and reported to the authorities. A data breach is completely different from a bug bounty program as it is not authorized and is done to damage/acquire data using unethical means.





0 comments:
Post a Comment